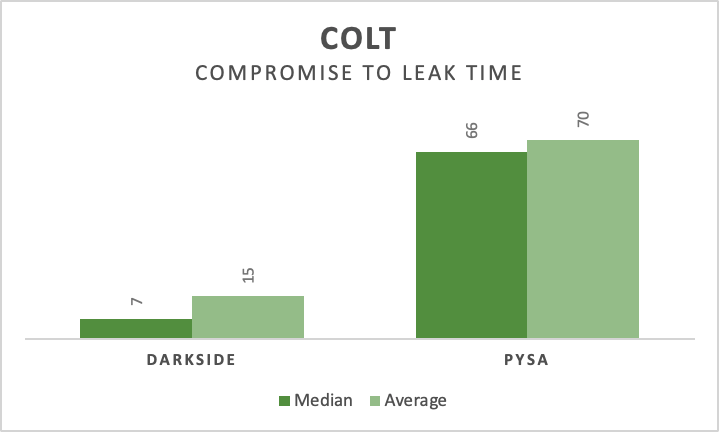
Ransomware, data theft and leaks. I do not plan on making this a ransomware-focused blog, but let us be honest, ransomware is just so prevalent that you cannot escape it. After my last blog and from private discussions, people working incident response cases in ransomware often are faced with the question: “When will the threat […]
Continue ReadingRansomware and Data Leak Site Publication Time Analysis
Learn at what times ransomware and data leak site operators are publishing victims on their dark web sites.
Continue ReadingIntroducing “Yara Scan Service” – Test Your Yara Rules Online
Did it happen to you that you wanted to quickly test a Yara rule you created, but you are missing a large enough data set to test your rule against? This is exactly what Yara Scan is designed for. You submit your Yara rule to the service and a short while later you will receive […]
Continue ReadingObserved Malware Campaigns – October 2020
An output of my most recent script (see my post “Malicious Attachment Analysis Script“), is the ability to create statistics and the data-set to understand what kind of malware campaigns are being delivered by email attachments. In October 2020 I received a total of 76,888 emails (2,480 per day) to my spam traps. Obviously not […]
Continue ReadingMalicious Attachment Analysis Script
I love collecting malicious emails, samples and trying to make sense of it, create context and share back with the community. One way I do so is by sharing malicious email attachments to MalwareBazaar and VirusTotal and including context such as email sender, subjects and date information. Since doing that, I have heard a few […]
Continue ReadingMalwareBazaar by abuse.ch – Python Scripts
MalwareBazaar is a project operated by abuse.ch. The purpose of the project is to collect and share malware samples, helping IT-security researchers and threat analyst protecting their constituency and customers from cyber threats. abuse.ch MalwareBazaar Now that abuse.ch has launched their newest service, the MalwareBazaar I am very happy to share some of the python […]
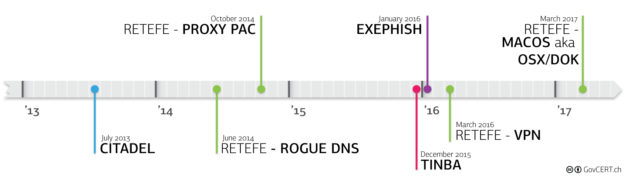
Continue ReadingAnalysing “Retefe” with Sysmon and Splunk
I recently took a closer look at Retefe because they seem to have abandon the short-lived “SmokeLoader”-phase and moved back to “socat.exe” and the TOR-network. The original delivery method is by mail spam, sending an Office document (either a docx or xlsx attachment) with an embedded OLE object (the malicious .exe file). If the victim […]
Continue ReadingCelebrating The 100th Shared MISP Event
Today marks a big day for the security research and protection effort here at vulnerability.ch: We just created and shared our 100th event with the wider MISP community. Thanks to the inclusion of our research at the MISP community provided by CIRCL, we have been able to share and consume indicators of compromise (IOCs) from […]
Continue ReadingEconomics of “Sextortion” Mails
For the past few months (it started in July 2018), I have been collecting Bitcoin wallet addresses from so called “extortion” or “sextortion” emails. The addresses have been added to my MISP server and is shared with other researchers to investigate or detect additional mails. CIRCL now has used the data to generate an analysis […]
Continue ReadingExtracting HTML Body From Firefox Cache
Today I was asked for a copy of a website that was already nuked before the analysis was completed. No online platforms has yet picked up a copy and VirusTotal did not show a hash for the download. Trying to come up with a solution for this problem, I remembered that browsers often keep a […]
Continue Reading